其它规则
- 当基本firewalld语法规则不能满足要求时,可以使用以下更复杂的规则
- rich-rules 富规则,功能强,表达性语言
- Direct configuration rules 直接规则,灵活性差
- 帮助:man 5 firewalld.direct
管理rich规则
- rich规则比基本的firewalld语法实现更强的功能,不仅实现允许/拒绝,还可以实现日志syslog和auditd,也可以实现端口转发,伪装和限制速率
- rich语法:
rule
[source]
[destination]
service|port|protocol|icmp-block|masquerade|forward-port
[log]
[audit]
[accept|reject|drop]
man 5 firewalld.richlanguage
- man 5 firewalld.richlanguage
规则
- 规则实施顺序:
- 该区域的端口转发,伪装规则
- 该区域的日志规则
- 该区域的允许规则
- 该区域的拒绝规则
- 每个匹配的规则生效,所有规则都不匹配,该区域默认规则生效
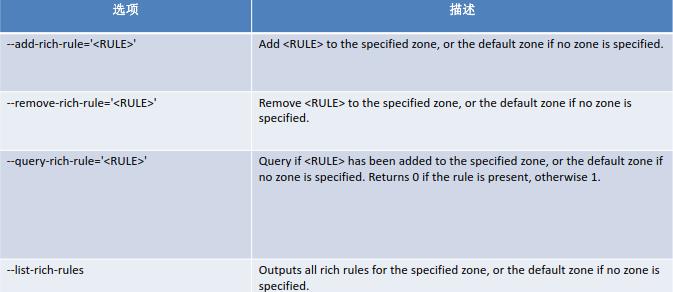
rich规则选项
rich规则示例
- 拒绝从192.168.0.11的所有流量,当address 选项使用source 或 destination时,必须用family= ipv4 |ipv6
firewall-cmd –permanent –zone=classroom –add-rich-rule=’rule
family=ipv4 source address=192.168.0.11/32 reject‘
- 限制每分钟只有两个连接到ftp服务
firewall-cmd –add-rich-rule=‘rule service name=ftp limit value=2/m accept’
- 抛弃esp( IPsec 体系中的一种主要协议)协议的所有数据包
firewall-cmd –permanent –add-rich-rule=’rule protocol value=esp drop’
- 接受所有192.168.1.0/24子网端口5900-5905范围的TCP流量
firewall-cmd –permanent –zone=vnc –add-rich-rule=’rule family=ipv4
source address=192.168.1.0/24 port port=5900-5905 protocol=tcp accept’
rich日志规则
- log [prefix=”
” [level= ] [limit value=” “] 可以是emerg,alert, crit, error, warning, notice, info, debug. s:秒, m:分钟, h:小时, d:天 - audit [limit value=”
“]
rich日志规则实例
- 接受ssh新连接,记录日志到syslog的notice级别,每分钟最多三条信息
firewall-cmd –permanent –zone=work –add-rich-rule=’rule service
name=”ssh” log prefix=”ssh ” level=”notice” limit value=”3/m” accept
- 从2001:db8::/64子网的DNS连接在5分钟内被拒绝,并记录到日志到audit,每小时最大记录一条信息
firewall-cmd –add-rich-rule=’rule family=ipv6 source
address=”2001:db8::/64″ service name=”dns” audit limit value=”1/h” reject’ –timeout=300
规则示例
- firewall-cmd –permanent –add-rich-rule=’rule family=ipv4 source address=172.25.X.10/32 service name=”http” log level=notice prefix=”NEW HTTP ” limit value=”3/s” accept’
- firewall-cmd –reload
- tail -f /var/log/messages
- curl http://serverX.example.com
伪装和端口转发
- NAT网络地址转换,firewalld支持伪装和端口转发两种NAT方式
- 伪装NAT
- firewall-cmd –permanent –zone=
- firewall-cmd –query-masquerade 检查是否允许伪装
- firewall-cmd –add-masquerade 允许防火墙伪装IP
- firewall-cmd –remove-masquerade 禁止防火墙伪装IP
- 示例:
- firewall-cmd –add-rich-rule=’rule family=ipv4 address=192.168.0.0/24 masquerade’
端口转发
- 端口转发:将发往本机的特定端口的流量转发到本机或不同机器的另一个端口。通常要配合地址伪装才能实现
- firewall-cmd –permanent –zone=
–add-forward-port=port= :proto= [:toport= ][:toaddr= ] 说明:toport= 和toaddr= 至少要指定一个 - 示例:
- 转发传入的连接9527/TCP,到防火墙的80/TCP到public zone 的192.168.0.254
- firewall-cmd –add-masquerade 启用伪装
- firewall-cmd –zone=public –add-forward-
- port=port=9527:proto=tcp:toport=80:toaddr=192.168.0.254
rich规则
- rich规则语法:
- forward-port port=
protocol=tcp|udp [to-port= ] [to-addr=] - 示例:
- 转发从192.168.0.0/24来的,发往80/TCP的流量到防火墙的端口8080/TCP
firewall-cmd –zone=work –add-rich-rule=’rule family=ipv4 source address=192.168.0.0/24 forward-port port=80 protocol=tcp to-port=8080′
rich规则示例
- firewall-cmd –permanent –add-rich-rule ‘rule family=ipv4 source address=172.25.X.10/32 forward-port port=443 protocol=tcp to-port=22’
- firewall-cmd –reload
- ssh -p 443 serverX.example.com
转载请注明:黑夜 » Linux之iptables(六、rich规则)
